Sean Verity is one of those interesting folks whose name fits his job, whose job fits his passion, and who took an unusual path to get there.
The word verity means a true principle or belief of fundamental importance. Verity is an ethical hacker, whose job is to stay at least one step ahead of those who would wage cyberwar on his employer, Michigan State University Federal Credit Union ($4.5B, East Lansing, MI).
Music and the Marines were first stops for Verity, who developed his white-hat hacking skills as a hobby before trying it out at work. Here, he tells his story and shares more about the role of ethical hacking manager at the world’s largest university-sponsored credit union.
Describe your history with MSUFCU and the development of the ethical hacking function.
Sean Verity: My journey began with a handful of ethical hacking projects after I was hired as an IT auditor in 2011. The success of those projects and the development of our internal strategies led to the creation of the ethical hacking department in 2016. I was the first ethical hacking specialist.
In 2018, I was promoted to manager, and we hired an ethical hacking specialist who reports to me. I report to the chief risk officer.
Why did MSUFCU create this role?
SV: Early on in my career at the credit union, we were preparing to migrate our home banking solution to a platform we had coded in-house from the ground up. Around that time, I was learning about ethical hacking on my personal time by hacking systems that I built in a lab at my house.
While we were having conversations at MSUFCU about what we should do to verify the security of the new platform, I asked my supervisor if I could conduct a penetration test and demonstrated that internal ethical hacking assignments could be valuable. Over time, my role has progressed from ad hoc testing, to testing full-time, to developing a comprehensive ethical hacking program.
Did MSUFCU create this role specifically for you?
SV: I was in the right place at the right time. That role did not exist when I was hired, and ethical hacking was not in my job description. I feel fortunate that my supervisor took a risk in allowing me to conduct that first penetration test and continues to see value in ethical hacking as a tool to improve the cybersecurity posture of MSUFCU.
Job titles say as much about the organization as they do the person. The “What’s In A Name” series on CreditUnions.com dives into notable, important, interesting, or just plain fun roles to find out what’s happening at the ground level and across the industry. Browse the whole series only on CreditUnions.com.
What made you a great fit for this job?
SV: That’s an interesting question because I didn’t set out to make a career in anything related to IT, let alone cybersecurity. My bachelor’s degree is in music education, and I spent a year as a public school band and choir director. Realizing that wasn’t my career path, I joined the United States Marine Corps and served as a communications officer for five-and-a-half years.
As a marine, I started to develop my leadership skills and gained exposure to IT and cybersecurity. I took an interest, my wife would call it an obsession, in ethical hacking. I’ve seen and met people who took similarly unexpected paths to this field. The one common characteristic I’ve observed is an intense curiosity for discovering ways to make things do stuff they were not designed to do.
Over the years, MSUFCU has generously invested in my development by allowing me to attend SANS courses and attain the GXPN, GPEN, and GAWN ethical hacking certifications. On numerous occasions, I have applied technical knowledge gained from these courses to identify and exploit vulnerabilities in MSUFCU’s environment.
Writing and planning are also important skills in my role. The Master of Science in Cybersecurity and Information Assurance program at Western Governors University developed my planning and writing abilities to make me more effective in my role.
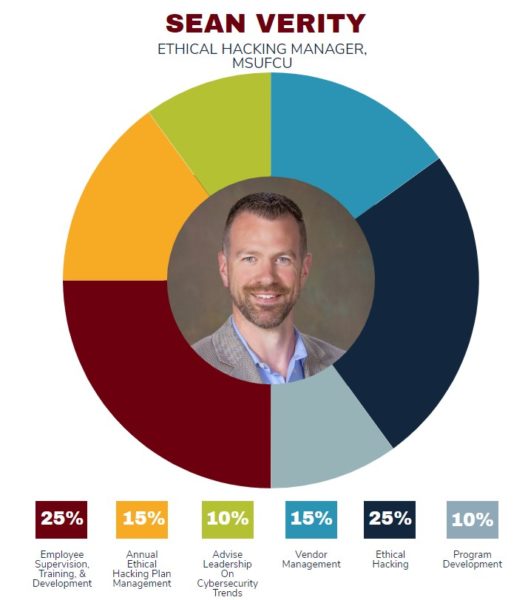
What are your areas of responsibility?
SV: Every year, I create a roadmap of ethical hacking projects. As the year progresses and new technology initiatives are introduced, we regularly collaborate with our business partners to ensure the test plan is aligned to MSUFCU’s strategic initiatives. I also perform ethical hacking projects that are more specialized or for products and services that will have a significant impact on MSUFCU.
I also oversee the development testing procedures and communication standards. A good deal of program development time is spent in identifying emerging attack techniques that could be used against the credit union. Our job is to assess MSUFCU’s exposure so we can implement protections before an attacker could exploit them.
How do you work with others?
SV: MSUFCU has an Information Security Committee that meets quarterly. It comprises the CEO, CIO, CRO, CISO, and me. I provide updates to the ethical hacking plan, discuss any significant vulnerabilities we identified, detail our team’s phishing training statistics, and cover cybersecurity issues or trends that could impact MSUFCU. We inform the board of directors by including a copy of this memorandum in the board report.
We also work with several third-party vendors. To ensure the quality of these services, I identify, establish, and develop relationships with qualified vendors that provide penetration testing and vulnerability scanning products and services.
Over time, my role has progressed from ad hoc testing, to testing full-time, to developing a comprehensive ethical hacking program.
What’s your daily routine?
SV: At the beginning of the week, I identify tasks or projects for my department to complete by the end of the week. In the morning, I look at that list and plan the day based on the priorities for the week. After that, I like to check in with my employee to see how things are going and to touch base on his projects. The rest of the day is a mix of responding to email, participating in meetings, planning, research, and hacking.
How does your role fit into the overall approach to risk management at MSUFCU?
SV: I read a study recently that stated the average cost to recover from a data breach is $4 million. That would be a huge hit to the bottom line of any credit union, not to mention the loss of trust with the membership.
To mitigate the risk of a data breach, the credit union has implemented numerous layers of information security controls that cybercriminals need to navigate to be effective. My department collaborates with IT to validate the effectiveness of its information security controls by modeling adversarial activity.
As MSUFCU continues to mature its information security program, it becomes more expensive for cybercriminals to attack MSUFCU. Our goal is to deter cybercriminal activity by making it unreasonably expensive to go after us.
What are your biggest challenges and how do you address them?
SV: Information security has been a priority for as long as I have been employed at MSUFCU. In my experience, our leadership has been supportive and receptive to developing an ethical hacking program.
I can think of a recent problem we solved, though, where empathy and understanding contributed to a positive outcome. IT implemented an important information security control a while back that we had recommended. After migrating one of our internal systems, we learned the security control, which we had recommended, was limiting functionality of the new system. A solution to accommodate the new system without disabling the control entirely was not entirely obvious.
It took some investigation and time to identify an appropriate solution. Fortunately, all stakeholders involved in solving this problem were transparent, cooperative, and patient. As a result, we were able to identify a solution that accommodates the new system without regressing MSUFCU’s cybersecurity posture.
I’ve seen and met people who took similarly unexpected paths to this field. The one common characteristic I’ve observed is an intense curiosity for discovering ways to make things do stuff they were not designed to do.
What is the best advice you can give other credit unions as they take on the challenges of cybersecurity?
SV: Accept that cybersecurity is an area that needs to be continuously evaluated and invested in because cybercriminals are continuously evaluating and investing in ways to bypass your cybersecurity controls.
How do you track success in your job? What makes you confident your own hacking is effective?
SV: As an ethical hacker, it’s always exciting to discover or exploit a significant vulnerability. However, as MSUFCU’s cybersecurity posture has matured over the years, significant vulnerabilities are becoming much harder to come by, which is a good thing. This is a good indication that MSUFCU is effectively investing resources to proactively reduce our exposure to cybercriminal activity.
There are a few reasons I’m confident in our testing program. We follow best-practice testing frameworks to ensure our testing is rigorous and comprehensive. We develop our proficiency through specialized training and by regularly attending some of the best hacker conferences available. Finally, our third-party testers are telling us our systems are secure. I see their opinions as independent validation of our efforts when they also have a hard time getting into our systems.
How do you stay current with topics that fall under your role?
SV: Blogs and Twitter are both great resources for the latest and greatest attack techniques. I have also dabbled in bug bounty programs to stay sharp. Training and certifications are helpful the SANS courses have been very beneficial. I also enjoy attending hacking conferences for example, Grrcon, Defcon, Derbycon, and Blackhat to network with other ethical hackers and to learn about new techniques.
This interview has been edited and condensed.